
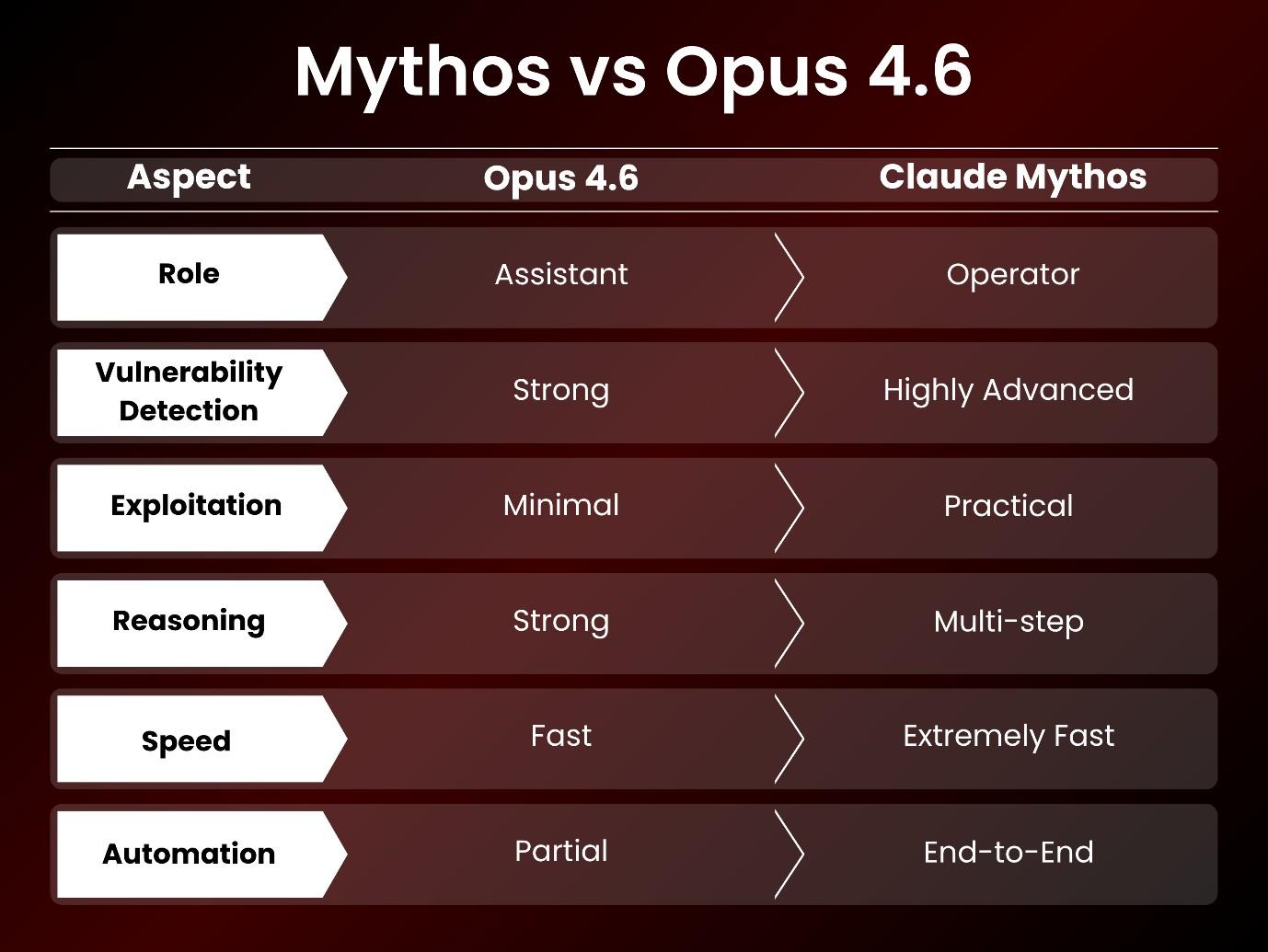
The integration of Artificial Intelligence into our security operations has been gradual but continuous. However, developments in AI show a larger shift happening before our eyes. In comparing Claude Mythos against Opus 4.6, we are doing much more than looking at performance scores of the two AI; rather we are observing a transformational change in how AI operates in the Security Operational environment.
For many years we have had AI assist our Security Operations teams with identifying vulnerabilities, sorting threat intelligence, and automating repetitive tasks, now we are beginning to see an AI evolve beyond a supportive role within Security Operations. It is entering a space where it can independently reason, simulate complex scenarios, and act.
If you manage risk or lead a security team, this transition is exactly what makes the gap between these two models worth your attention.
A Quick Look at the Two Models
To understand where we are going, we first need to look at what we are working with right now.
Claude Opus 4.6 represents the standard that most organizations rely on. It is stable, reliable, and built to slide perfectly into existing enterprise workflows. When it comes to AI in cybersecurity, Opus 4.6 plays the role of an incredibly smart assistant. It helps your team review sprawling codebases, spot common vulnerabilities, and automate the repetitive tasks that eat up your day. Because its outputs are highly predictable, it thrives in environments where control and strict consistency matter most.
Claude Mythos takes a completely different path. It is built from the ground up for deep technical reasoning, specifically tailored for complex, layered cybersecurity challenges. Instead of waiting for prompts to assist you, it operates with a surprising degree of independence.
Here is what Mythos brings to the table:
- Analyses vast network environments holistically.
- Identifies hidden, obscure weaknesses.
- Simulates realistic attack scenarios with almost zero initial input.
- This core difference in design philosophy is where the gap between the two models begins.
The Real Difference Lies in Depth
One of the sharpest contrasts between these two cybersecurity tools is how they handle vulnerability discovery.
Opus 4.6 shines when it deals with known patterns and standard security issues. Give it a codebase, and it will quickly flag risks and suggest solid improvements. For your day-to-day security checklist, this capability is fantastic.
But as you know, modern enterprise systems are rarely straightforward. We build them on complex layers of microservices, third-party integrations, and intricate logic flows. In these environments, the most dangerous vulnerabilities do not sit out in the open. They hide in edge cases, buried dependencies, and subtle misconfigurations.
This is where Mythos flexes its muscles. It processes massive, tangled systems effectively. It excels at deep vulnerability analysis, finding the non-obvious weaknesses that traditional scanners miss. Rather than looking at an isolated bug, Mythos analyses the relationships across your entire infrastructure. It looks at how a minor issue in one container connects to a larger flaw in your database structure.
The end result? A much deeper, comprehensive understanding of your actual risk surface.
From Identifying Problems to Understanding Impact
Finding a bug is only half the battle. What happens after a vulnerability is found highlights another major difference between the models.
Opus 4.6 does a great job explaining the issue and why it matters. It gives your team the context they need and suggests possible fixes, helping you make informed, rapid decisions.
Mythos takes this process several steps further. It does not just point at the broken window; it shows you exactly how a burglar could climb through it. Mythos actively constructs logical attack paths. It demonstrates how a seemingly low-severity weakness in a peripheral system could be chained together to gain root access to your core servers.
The change from identifying a flaw to understanding what an adversary can do with that flaw is huge. Cybersecurity threats do not simply mean there is a vulnerability. The actual threat is based on the ease in which an adversary can carry out an attack on a vulnerability. By providing this context, Mythos is able to provide you with a realistic and sometimes, disturbing, picture of threat potential.
Thinking in Terms of Real Attacks
Cyberattacks are almost never isolated events. Threat actors move laterally, stack exploits, and exploit a chain of small weaknesses to achieve their goals. To defend against this, your tools need to think sequentially. They must connect disparate pieces of information just like a human attacker would.
Mythos shows incredible strength in this arena. It naturally maps out how vulnerabilities interact and simulates multi-step attack scenarios. It delivers insights that mirror real-world threat behavior. This allows your organization to stop playing whack-a-mole with individual issues and start dismantling systemic risks.
Opus 4.6 is a highly capable tool, but it focuses heavily on individual tasks. It does not naturally extend into full, multi-staged attack simulation without heavy human guidance.
Speed Is Changing the Game
Time is always working against us in security. Traditional workflows involve distinct stages: discovery, validation, testing, and remediation. Because we usually handle these steps separately, response times can drag.
Opus 4.6 accelerates parts of this workflow, specifically when it comes to analyzing data and documenting findings. Mythos, however, merges these stages into a fluid, continuous process. It spots vulnerabilities, assesses their real-world impact, and helps validate the fixes in a fraction of the time.
This does not just boost efficiency. It fundamentally changes how your security team operates. Faster insights lead to faster decisions. When you are staring down a potential breach, speed is the only thing standing between successful prevention and a massive incident response effort.
Why This Gap Matters for Organizations
The difference between these approaches goes far beyond the performance of technical metrics. They have a significant influence on your overall security posture.
On the positive side, cutting-edge (advanced) artificial intelligence can enhance your protective measures. It's estimated that you can reduce the time spent on completing vulnerability assessments by a significant amount of time, and the accuracy of these assessments will also be enhanced, which will allow you to transition from reactive to proactive measures. You will be able to proactively search for threats and determine what they could be before they find you.
On the negative side, if malicious actors obtain access to advanced capabilities, the risks are very significant. Autonomous AI has the potential to speed up exploit development and provide novice hackers with an easier way to commit cybercrime, resulting in an exponential increase in attacks and scale of cybercrime.
Therefore, the duality of advanced artificial intelligence in cybersecurity is what makes it both extremely effective and highly sensitive.
A Reason for Controlled Adoption
You might wonder why models like Mythos are not available to everyone just yet. The limited number of AI applications indicates the industry is taking a measured and careful route. Limiting access to organizations affords them the opportunity to assess the actual effects of these tools prior to their general release. This also demonstrates an urgent issue for the entire industry. As AI capabilities continue to advance at an astonishing pace, the associated policies, safety frameworks, and guidelines are struggling to keep up. We must bridge the gap between capability and control.
What Should Security Teams Do Next?
You do not need to rip out your existing systems overnight. Instead, focus on preparing your team for the inevitable shift.
Here is how you can start:
- Integrate gradually: Bake AI-driven cybersecurity tools into your existing development pipelines.
- Shift to continuous monitoring: Move away from fixed-interval testing and use AI for real-time threat analysis.
- Educate your team: Ensure your security professionals understand how autonomous AI operates, how threat actors might use it, and how to interpret complex AI outputs.
Is Opus 4.6 Still Enough?
Given all of the advancements from Mythos, you may believe that Opus 4.6 is outdated, but that is not the case. Opus 4.6 is still very much relevant.
Opus 4.6 provides an extremely stable, consistent, and reliable system for the vast majority of real-life applications where an assistant can streamline security operations on a day to day basis.
Mythos represents an evolved version of your existing tools, not something to replace your current tools right away. Instead, Mythos will help provide you with insight into how to use cybersecurity tools in the immediate future.
The contrasting nature of Claude Mythos and Opus 4.6 clearly indicates the future direction of our industry. The expansion of AI's power in the realm of cybersecurity has become apparent through its transformation from a support system to an independent entity that can make decisions based upon analyses of the most complex cyber environments.
This transformation is providing return on investment with respect to speed, efficiency and depth; however, it also presents new challenges that require an intelligent approach with an appropriate design strategy. Cybersecurity platforms are moving toward being increasingly dynamic and automated with changes occurring at a rapid pace. To remain secure, organizations must employ appropriate tools while modifying their overall strategies to keep up with the rate of change.
The disparity between these two models represents not only a noticeable trend to follow, but also it represents the future of security and that organizations need to begin preparing for this right now.
Prepare for the Next Shift in AI Security
Integrate gradually, shift to continuous monitoring, and educate your team for controlled adoption.
Talk to CyberCube