
Healthcare applications continue developing rapidly. Telehealth and AI are just two examples where innovation is happening all around us. However, one consistent problem exists: security does not seem to have caught up with technology. This implies that, in addition to being a technical issue, there is also a compliance concern. As soon as your application interacts in any way with patient records, it is subject to the requirements of HIPAA.
Want to reduce HIPAA exposure risk?
Start with data visibility, secure APIs, enforce strong access controls, and validate vendor BAAs.
The Importance of HIPAA Compliance in 2026
In 2026 HIPAA will not only minimize the possibility of a data breach but how your entire system connects and interacts with each other. Regulators want to clearly see every element of your data flow system; therefore, there should be proper access controls, vendor accountability and auditing processes in place.
You cannot simply claim your environment is secure, you must continue to demonstrate it. All while consuming HIPAA data will be more complex than ever due to more APIs, cloud infrastructure, third party vendors, and AI Integration; thus, the number of points of exposure significantly increases - and with it, the likelihood of being cited for a violation also increases.
Most companies don’t knowingly violate HIPAA. They just assume things. But HIPAA doesn’t work on assumptions - it works on exposure. If your system can access, process, or transmit PHI, you are responsible.
The Most Common HIPAA Mistakes in 2026
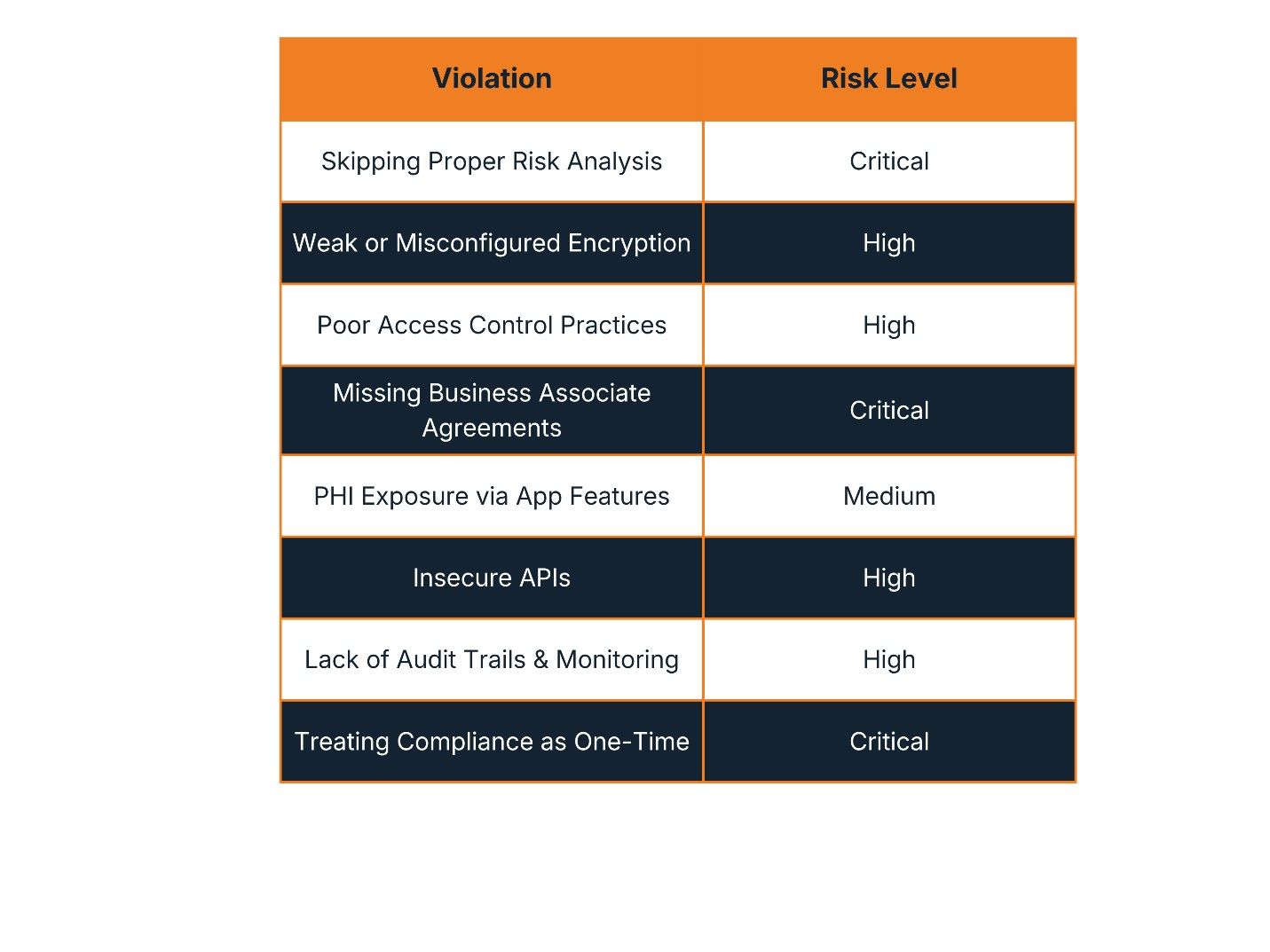
The table below outlines the eight most prevalent HIPAA compliance failures seen in healthcare applications today, along with their risk severity.
A Closer Look at Each Violation
1. Skipping Proper Risk Analysis
Risk analysis is the foundation of HIPAA and the most commonly ignored requirement. Many teams use generic templates, conduct it once, or skip it entirely. Without it, you don’t know where PHI is stored, how it flows through your system, or what vulnerabilities exist. Every other control becomes weak without this foundation. Risk Analysis exactly points out to where the actual risk might reside, so that it gets tackled efficiently.
2. Weak or Misconfigured Encryption
Encryption is often assumed to be handled - in reality, data is frequently encrypted in transit but not at rest. Sensitive data is stored locally on devices, and test environments often contain real patient data. These gaps create silent exposure that attackers can exploit.
3. Poor Access Control Practices
Common failures include shared accounts, excessive user privileges, and missing session timeouts. All it takes is one compromised credential. Without proper restrictions, attackers can move freely across systems, accessing far more than they should.
4. Ignoring Vendor Compliance (No BAAs)
Healthcare apps depend heavily on third-party tools - analytics platforms, cloud providers, communication APIs, and logging systems. If these vendors interact with PHI, they must sign a Business Associate Agreement (BAA). No BAA equals a direct HIPAA violation, regardless of how strong your internal controls are.
5. PHI Exposure Through Everyday Features
Not all violations come from hackers. Push notifications revealing medical details, logs storing sensitive data, and debug messages exposing user information are easy to overlook and very risky. These unintentional leaks often go unnoticed until a breach has already occurred.
6. Insecure APIs
APIs are essential but often poorly secured. Missing authentication, broken authorization checks, and predictable resource identifiers can expose patient records to unauthorized access - one of the most serious and frequently exploited HIPAA failures in modern healthcare applications.
7. Lack of Monitoring and Audit Trails
If something goes wrong, can you answer: “Who accessed what data, and when?” HIPAA requires detailed logging, continuous monitoring, and the ability to investigate incidents. Without full visibility into your systems, detection becomes impossible and breach response is severely delayed.
8. Treating Compliance as a One-Time Activity
Teams often prepare for one audit, complete the documentation, and move on. But systems evolve - new features are added, vendors change, and teams grow. Without continuous oversight, compliance quietly erodes between audits, leaving the organization exposed.
What should Health Care Applications be doing different?
Preventing HIPAA violations is more about starting off on the right foot and doing it right every time, then it is about doing more things than necessary. Here's how to avoid the top mistakes:
- Conduct regular, and thorough, risk assessments and document the flow of PHI data.
- Enforce encryption for both data at rest and in transit; never use an actual PHI value in a test environment.
- Implement strong access controls such as RBAC, MFA, session expiration, and least-privilege.
- Audit all third-party vendors and have them sign a BAA before accessing PHI data.
- Review notification messages, logs, and debug output to prevent accidental exposure of PHI.
- Secure APIs with authentication, authorization checks, and input validation.
- Implement real-time monitoring and dashboards with alerts and comprehensive audit logs.
- Implement an ongoing compliance program that includes regular reviews and training for employees.
What Good HIPAA Compliance Looks Like
Good HIPAA compliance is not just passing an audit or having policies in place. It requires five core pillars working together - and all of them are equally important.
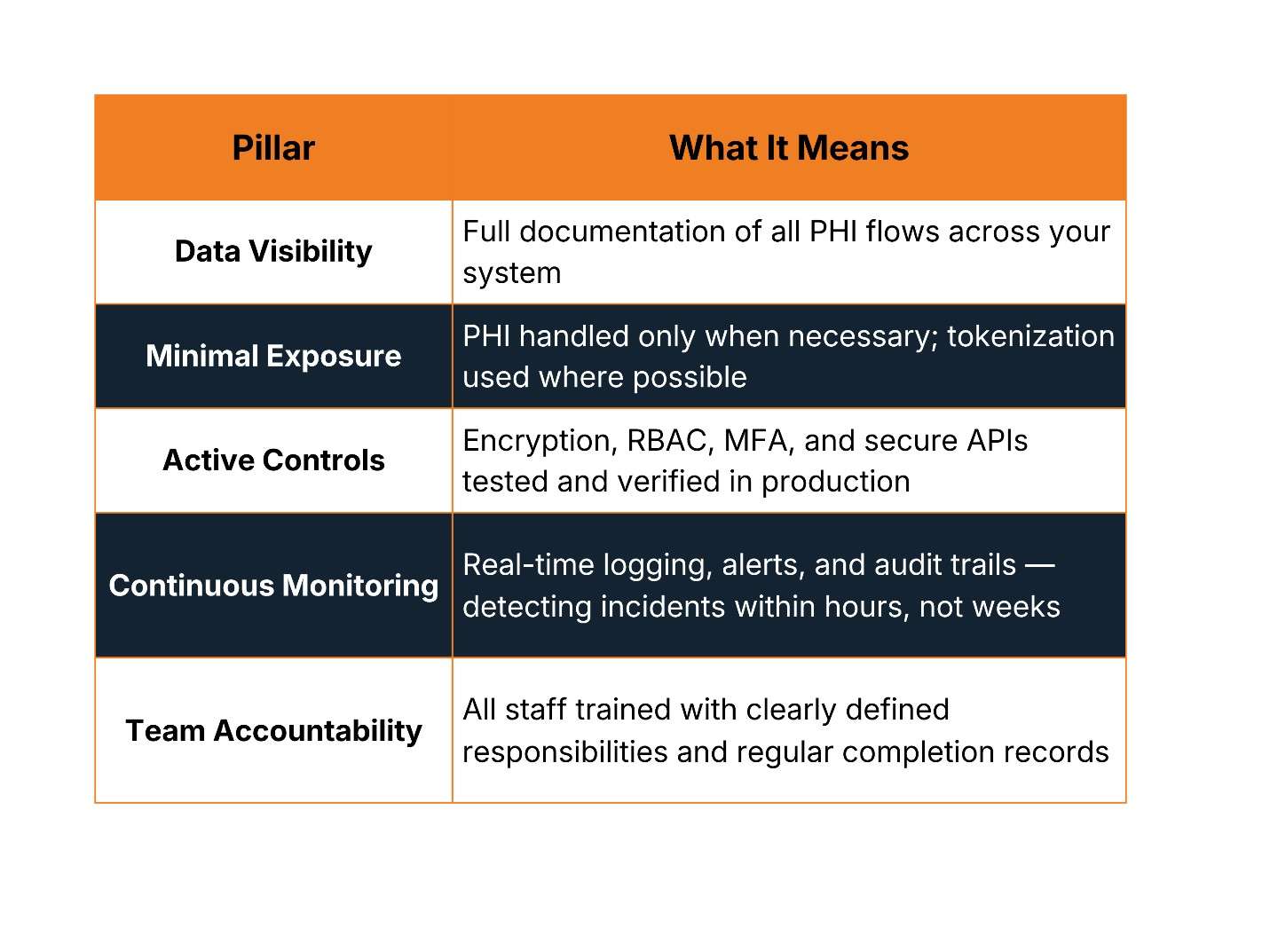
Reaching the optimized level isn’t a one-time achievement. Organizations move through stages - from reactive (fixing things after a breach), to aware (having basic policies), to structured (documented controls), to proactive (continuous monitoring), and finally to optimized (compliance embedded into company culture). The goal is to keep moving forward, not to declare victory.
The Bottom Line
Most HIPAA violations don’t happen because companies don’t care. They happen because companies move fast and assume security will catch up. It doesn’t.
The organizations that get it right design for compliance early, treat security as part of the product, and stay proactive instead of reactive. Because in healthcare, you’re not just building software. You’re handling patient trust - and once that trust is broken, it’s extremely hard to rebuild.
Start with data visibility. Reduce PHI exposure. Build security into your architecture. Take vendor risk seriously. Implement continuous monitoring. And accept that compliance is an ongoing commitment - not a one-time checkbox.
Reduce HIPAA Violation Risk in 2026
Start with data visibility. Reduce PHI exposure. Build security into your architecture. Take vendor risk seriously. Implement continuous monitoring.
Talk to CyberCube